-
Defensive Security Handbook: Best Practices for Securing Infrastructure
Despite the increase of high-profile hacks, record-breaking data leaks, and ransomware attacks, many organizations don’t have the budget to establish or outsource an information security (InfoSec) program, forcing them to learn on the job. For companies obliged to improvise, this pragmatic guide provides a security-101 handbook with steps, tools, processes, and ideas to help you drive maximum-security improvement at little or no cost.Each chapter in this book provides step-by-step instructions for dealing with a specific issue, including breaches and disasters, compliance, network infrastruc... [Read More]
- ASIN: 1491960388
- ASIN: 1491960388
- ISBN: 9781491960387
- Brand: OREILLY
- Manufacturer: O'Reilly Media
-
Information Security: Principles and Practices (Certification/Training)
Information Security: Principles and Practices, Second Edition Everything You Need to Know About Modern Computer Security, in One Book Clearly explains all facets of information security in all 10 domains of the latest Information Security Common Body of Knowledge [(ISC)² CBK]. Thoroughly updated for today’s challenges, technologies, procedures, and best practices. The perfect resource for anyone pursuing an IT security career. Fully updated for the newest technologies and best practices, Information Security: Principles and Practices, Second Edition thoroughly covers all 10 dom... [Read More]
- ASIN: B00KKNO8VO
- ASIN: B00KKNO8VO
- Manufacturer: Pearson IT Certification
-
CISSP (ISC)2 Certified Information Systems Security Professional Official Study Guide and Official ISC2 Practice Tests Kit
This value-packed packed set for the serious CISSP certification candidate combines the bestselling CISSP (ISC)2 Certified Information Systems Security Professional Official Study Guide, 7th Edition with an all new collection of Practice Exams to give you the best preparation ever for the high-stakes CISSP Exam. CISSP (ISC)2 Certified Information Systems Security Professional Official Study Guide, 7th Edition has been completely updated for the latest 2015 CISSP Body of Knowledge. This bestselling Sybex study guide covers 100% of all exam objectives. You'll prepare for the exam smarter and fas... [Read More]
- ASIN: 1119314011
- ASIN: 1119314011
- ISBN: 1119314011
- Brand: Sybex
- Manufacturer: Sybex
-
Microsoft Azure Security Center (IT Best Practices - Microsoft Press)
Discover high-value Azure security insights, tips, and operational optimizations This book presents comprehensive Azure Security Center techniques for safeguarding cloud and hybrid environments. Leading Microsoft security and cloud experts Yuri Diogenes and Dr. Thomas Shinder show how to apply Azure Security Center’s full spectrum of features and capabilities to address protection, detection, and response in key operational scenarios. You’ll learn how to secure any Azure workload, and optimize virtually all facets of modern security, from policies and identity to incident response and ri... [Read More]
- ASIN: B07D5J97JV
- ASIN: B07D5J97JV
- Manufacturer: Microsoft Press
-
CompTIA Security+ Get Certified Get Ahead: SY0-501 Study Guide
Pass the First Time.The CompTIA Security+ Get Certified Get Ahead SY0-501 Study Guide is an update to the top-selling SY0-201, SY0-301, and SY0-401 study guides, which have helped thousands of readers pass the exam the first time they took it. It covers all of the SY0-501 objectives and includes the same elements readers raved about in the previous two versions. Each of the eleven chapters presents topics in an easy to understand manner and includes real-world examples of security principles in action. The author uses many of the same analogies and explanations he’s honed in the classroom t... [Read More]
- ASIN: 1939136059
- ASIN: 1939136059
- ISBN: 1939136059
- Brand: YCDA, LLC
- Manufacturer: YCDA, LLC
-
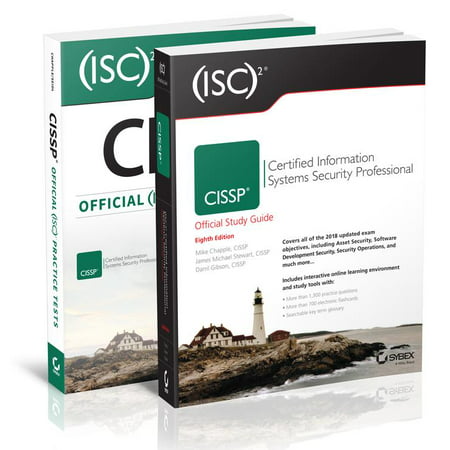
(ISC)2 CISSP Certified Information Systems Security Professional Official Study Guide, 8e & CISSP Official (ISC)2 Practice Tests, 2e
This value-packed packed set for the serious CISSP certification candidate combines the bestselling (ISC)² CISSP Certified Information Systems Security Professional Official Study Guide, 8th Edition with an all new collection of Practice Exams to give you the best preparation ever for the high-stakes CISSP Exam. (ISC)² CISSP Study Guide, 8th Edition has been completely updated for the latest 2018 CISSP Body of Knowledge. This bestselling Sybex study guide covers 100% of all exam objectives. You'll prepare for the exam smarter and faster with Sybex thanks to expert content, real-world examp... [Read More]
- ASIN: 1119523265
- ASIN: 1119523265
- ISBN: 1119523265
- Manufacturer: Sybex
-
AWS: Security Best Practices on AWS: Learn to secure your data, servers, and applications with AWS
Delve deep into various security aspects of AWS to build and maintain a secured environmentKey FeaturesLearn to secure your network, infrastructure, data, and applications in AWS cloudUse AWS managed security services to automate securityDive deep into various aspects such as the security model, compliance, access management and much more to build and maintain a secured environmentExplore Cloud Adoption Framework (CAF) and its componentsEmbedded with assessments that will help you revise the concepts you have learned in this bookBook DescriptionWith organizations moving their workloads, applic... [Read More]
- ASIN: 178913451X
- ASIN: 178913451X
- ISBN: 178913451X
- Manufacturer: Packt Publishing
-
The Book on Managing Rental Properties: A Proven System for Finding, Screening, and Managing Tenants With Fewer Headaches and Maximum Profit
No matter how great you are at finding good rental property deals, you could lose everything if you don’t manage your properties correctly! But being a landlord doesn’t have to mean middle-of-the-night phone calls, costly evictions, or daily frustrations with ungrateful tenants. Being a landlord can actually be fun IF you do it right. That’s why Brandon and Heather Turner put together this comprehensive book that will change the way you think of being a landlord forever. Written with both new and experienced landlords in mind, The Book on Managing Rental Properties takes you on an insid... [Read More]
- ASIN: B018W8HSP6
- ASIN: B018W8HSP6
- Manufacturer: BiggerPockets Publishing, LLC
-
Building a Comprehensive IT Security Program: Practical Guidelines and Best Practices
This book explains the ongoing war between private business and cyber criminals, state-sponsored attackers, terrorists, and hacktivist groups. Further, it explores the risks posed by trusted employees that put critical information at risk through malice, negligence, or simply making a mistake. It clarifies the historical context of the current situation as it relates to cybersecurity, the challenges facing private business, and the fundamental changes organizations can make to better protect themselves. The problems we face are difficult, but they are not hopeless.Cybercrime continues to grow ... [Read More]
- ASIN: 1484220528
- ASIN: 1484220528
- ISBN: 9781484220528
- Manufacturer: Apress
-
Information Governance: Concepts, Strategies and Best Practices (Wiley CIO)
The essential guide to effective IG strategy and practice Information Governance is a highly practical and deeply informative handbook for the implementation of effective Information Governance (IG) procedures and strategies. A critical facet of any mid- to large-sized company, this “super-discipline” has expanded to cover the management and output of information across the entire organization; from email, social media, and cloud computing to electronic records and documents, the IG umbrella now covers nearly every aspect of your business. As more and more everyday business is conducted el... [Read More]
- ASIN: 1119491444
- ASIN: 1119491444
- ISBN: 1119491444
- Manufacturer: Wiley
-
Foundations Of Information Security Based On ISO27001 And ISO27002 (Best Practice)
This book is intended for everyone in an organization who wishes to have a basic understanding of information security. Knowledge about information security is important to all employees. It makes no difference if you work in a profit- or non-profit organization because the risks that organizations face are similar for all organizations. It clearly explains the approaches that most organizations can consider and implement which helps turn Information Security management into an approachable, effective and well-understood tool. It covers: * The quality requirements an organization may have for ... [Read More]
- ASIN: 940180012X
- ASIN: 940180012X
- ISBN: 940180012X
- Brand: Van Haren Publishing
- Manufacturer: Van Haren Publishing
-
Attached: The New Science of Adult Attachment and How It Can Help YouFind - and Keep - Love
"A groundbreaking book that redefines what it means to be in a relationship."--John Gray, PhD., bestselling author of Men Are from Mars, Women Are from VenusWe already rely on science to tell us what to eat, when to exercise, and how long to sleep. Why not use science to help us improve our relationships? In this revolutionary book, psychiatrist and neuroscientist Dr. Amir Levine and Rachel Heller scientifically explain why why some people seem to navigate relationships effortlessly, while others struggle.Discover how an understanding of adult attachment—the most advanced relationship scie... [Read More]
- ASIN: 1585429139
- UPC: 619580015955
- ASIN: 1585429139
- ISBN: 1585429139
- Brand: Unknown
- Manufacturer: TarcherPerigee
-
Information Security Best Practices: 205 Basic Rules
Protecting computer networks and their client computers against willful (or accidental) attacks is a growing concern for organizations and their information technology managers. This book draws upon the author's years of experience in computer security to describe a set of over 200 "rules" designed to enhance the security of a computer network (and its data) and to allow quick detection of an attack and development of effective defensive responses to attacks. Both novice and experienced network administrators will find this book an essential part of their professional "tool kit." It is also es... [Read More]
- ASIN: 1878707965
- ASIN: 1878707965
- ISBN: 1878707965
- Brand: Brand: Butterworth-Heinemann
- Manufacturer: Butterworth-Heinemann
-
Self-Compassion: The Proven Power of Being Kind to Yourself
Kristin Neff, Ph.D., says that it’s time to “stop beating yourself up and leave insecurity behind.” Self-Compassion: Stop Beating Yourself Up and Leave Insecurity Behind offers expert advice on how to limit self-criticism and offset its negative effects, enabling you to achieve your highest potential and a more contented, fulfilled life.More and more, psychologists are turning away from an emphasis on self-esteem and moving toward self-compassion in the treatment of their patients—and Dr. Neff’s extraordinary book offers exercises and action plans for dealing with every emotionally d... [Read More]
- ASIN: B004JN1DBO
- ASIN: B004JN1DBO
- Brand: HarperCollins e-books
- Manufacturer: HarperCollins e-books
-
The Whole-Brain Child: 12 Revolutionary Strategies to Nurture Your Child's Developing Mind
NEW YORK TIMES BESTSELLER • The authors of No-Drama Discipline and The Yes Brain explain the new science of how a child’s brain is wired and how it matures in this pioneering, practical book. “Simple, smart, and effective solutions to your child’s struggles.”—Harvey Karp, M.D. In this pioneering, practical book, Daniel J. Siegel, neuropsychiatrist and author of the bestselling Mindsight, and parenting expert Tina Payne Bryson offer a revolutionary approach to child rearing with twelve key strategies that foster healthy brain development, leading to calmer, happier children. The a... [Read More]
- ASIN: 0553386697
- ASIN: 0553386697
- ISBN: 9780553386691
- Brand: Bantam
- Manufacturer: Bantam
-
(isc)2 Cissp Certified Information Systems Security Professional Official Study Guide, 8e & Cissp Official (Isc)2 Practice Tests, 2e
This value-packed packed set for the serious CISSP certification candidate combines the bestselling (ISC)² CISSP Certified Information Systems Security Professional Official Study Guide, 8th Edition with an all new collection of Practice Exams to give
- UPC: 326998267
-
Thriving from A to Z : Best Practices to Increase Resilience, Satisfaction, and Success
Thriving from A to Z provides you with 26 best practices proven to help you learn, grow, and succeed. The essential best practices, valuable implementation tips, and engaging reflection activities help you build resilience and
- UPC: 662577702
-
Operationalizing Information Security: Putting the Top 10 SIEM Best Practices to Work - eBook
Applying a top 10 best practices approach to leverage security information event management (SIEM), this e-book offers infosec professionals the means to gain more assured value from SIEM. Whether seeking to streamline incident response, automate
- UPC: 917148583
-
Defensive Security Handbook : Best Practices for Securing Infrastructure
Despite the increase of high-profile hacks, record-breaking data leaks, and ransomware attacks, many organizations don't have the budget to establish or outsource an information security (InfoSec) program, forcing them to learn on the job. For
- UPC: 55479617
-
Becoming an Independent Security Consultant : A Practical Guide to Starting and Running a Successful Security Consulting Practice
The demand for security consulting services is at an all-time high. Organizations of all types face unprecedented challenges in dealing with workplace violence, internal and external theft, robbery and crimes of all varieties. These organizations
- UPC: 350951682
-
Implementing Diversity: Best Practices for Making Diversity Work in Your Organization
This practical and provocative guide provides the strategies and tactics used by organizations committed to implementing diversity from the top down. Focusing on the necessity for a strategic change initiative, Loden discusses: how to position
- UPC: 25455699
-
Essentials of Health Information Management : Principles and Practices
Get in the know and learn in the now with ESSENTIALS OF HEALTH INFORMATION MANAGEMENT: PRINCIPLES AND PRACTICES, FOURTH EDITION! Electronic health records are the norm in health care today, so you must master technology
- UPC: 435003780
-
Building a World-Class Compliance Program : Best Practices and Strategies for Success
Written by a long-standing practitioner in the field, this timely and critical work is your best source for understanding all the complex issues and requirements associated with corporate compliance. It provides clear guidance for those
- UPC: 8041910
Cybersecurity Best Practices Part 1 - Preventing Opportunistic Attacks in 5 Easy Steps
Information Security Best Practices
Microsoft shares tips on how to secure your identity against cybersecurity threats
© 10Toply.com - all rights reserved - Sitemap 10Toply.com is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com